Credential Data Privacy: The Executive Guide to Secure Issuance in 2026
Published on March 20, 2026

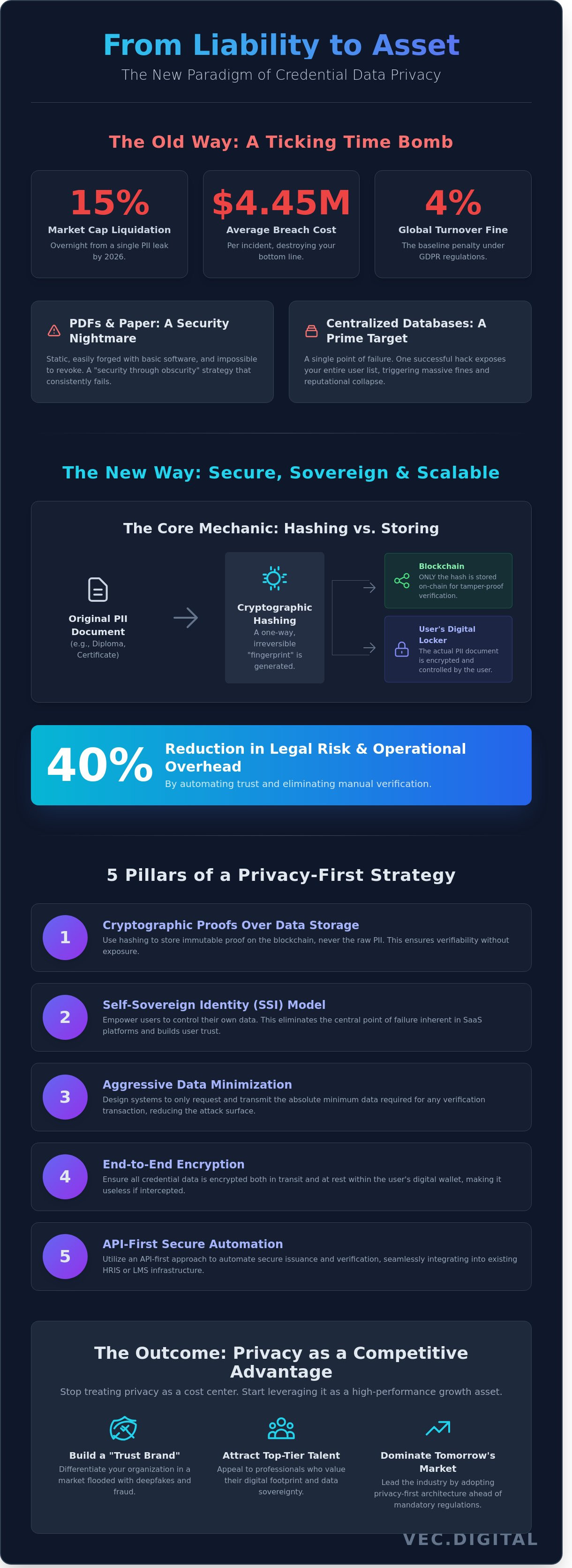
In 2026, a single PII leak won't just cost you a fine; it will liquidate your brand's market cap by 15% overnight. Most executives still treat credential data privacy as a defensive tax or a legal hurdle that slows down operations. You've likely felt the friction of navigating the 120+ unique global privacy regulations that now dictate how you issue and store digital records. It's a bottleneck that eats into your margins and stalls your ability to scale.
We're here to flip that script. This guide shows you how to transform security from a compliance burden into a high-performance growth asset. You'll learn how to implement blockchain-based issuance that's 100% tamper-proof while slashing your legal risk and operational overhead by 40% compared to legacy databases. We're moving past the "public ledger" myths to show you the exact architecture that secures your reputation and your bottom line.
We'll break down the transition from vulnerable PII silos to a decentralized framework that actually accelerates your business.
Key Takeaways
- Stop treating credential data privacy as a compliance burden and start leveraging it as a high-performance asset for scalable growth.
- Master the cryptographic "Hashing vs. Storing" distinction to ensure maximum data security without sacrificing the verifiability of your digital records.
- Upgrade from baseline GDPR compliance to a Self-Sovereign model to remove the single point of failure inherent in centralized SaaS platforms.
- Implement a 5-pillar technical strategy that prioritizes data minimization and encryption to protect your organization from reputational damage.
- Learn how an API-first approach can automate secure issuance while seamlessly integrating into your existing HRIS or LMS infrastructure.
Why Credential Data Privacy is Your Organization’s Biggest Liability (and Opportunity)
Credential data privacy isn't a compliance checkbox; it's a core business asset. It refers to the secure management and protection of Personally Identifiable Information (PII) embedded within digital badges, certificates, and diplomas. If you're still treating credentials as simple image files, you're bleeding money. Data breaches in 2023 cost an average of $4.45 million per incident according to IBM. For organizations issuing certifications, a single "leaky" database doesn't just trigger GDPR fines. It kills your brand's authority. Trust takes years to build and seconds to incinerate when a forged PDF surfaces on LinkedIn.
2026 marks a hard pivot for the industry. New global regulations, including the full rollout of the EU’s Digital Identity Wallet, will mandate privacy-first architectures. Companies that fail to adapt by this deadline will find themselves locked out of international markets. We're moving away from vanity metrics like "total badges issued" which mean nothing for the bottom line. High-growth organizations now focus on trust metrics. These are measurable indicators of data integrity and verification speed that drive long-term ROI. Secure credential data privacy ensures your certificates are assets that scale, not liabilities that drain your legal budget.
The Hidden Risks of Traditional Paper and PDF Certificates
PDFs are a security nightmare. They're static, easy to forge with basic editing software, and nearly impossible to revoke once they're sent. Relying on them is "security through obscurity," a strategy that fails every time in a digital-first economy. Centralized databases housing this information are prime targets for SQL injections. When a hacker hits a central server, they don't just get one name; they get your entire alumni or employee list. This centralized vulnerability is why smart organizations are moving toward decentralized models like Self-sovereign identity (SSI). This technology ensures the individual, not a vulnerable central server, holds the keys to their data.
Privacy as a Competitive Advantage for Universities and NGOs
Forward-thinking universities and NGOs use data sovereignty to attract top-tier talent. Students and professionals in 2024 value their digital footprint. They want to know their achievements won't be sold or leaked. Building a "Trust Brand" is the only defense against the rise of deepfakes and sophisticated credential fraud. Transitioning to secure, encrypted credentialing isn't just about safety; it's about the bottom line. Organizations implementing automated credential data privacy systems report a 40% reduction in administrative overhead. You're no longer wasting hundreds of man-hours manually verifying degrees over the phone or email. Automation handles the trust, while you focus on scaling your impact and profit.
Every certificate you issue is a piece of data that can either build your reputation or destroy your balance sheet. Choosing a privacy-first approach isn't just about avoiding the 4% global turnover fine under GDPR; it's about positioning your organization as a leader in the digital economy. The market doesn't reward those who wait for regulations to catch up. It rewards the innovators who secure their data today to dominate tomorrow.
The Mechanics of Privacy: How Blockchain Protects PII without Sacrificing Verifiability
The biggest misconception in the tech world is that blockchain is a public billboard for your personal data. It's not. If you're building a system that puts raw Personally Identifiable Information (PII) on a public ledger, you're doing it wrong and inviting a GDPR disaster. In 2024, the average cost of a data breach hit $4.88 million. Smart businesses don't store data on-chain; they store proof. This is the foundation of modern credential data privacy.
The magic happens through hashing. Instead of uploading a 5MB diploma or a high-resolution ID scan, the system generates a cryptographic fingerprint called a hash. This hash is a one-way string of characters. You can't reverse-engineer the original document from it. The blockchain only records this fingerprint and its status. The actual document lives in a "Digital Locker" or an encrypted mobile wallet controlled by the user. This separation of concerns ensures that even if a hacker targets the blockchain, they find nothing but useless strings of code.
Verification becomes a matter of seconds, not weeks. When a user presents a QR code for validation, the verifier's system compares the presented document against the on-chain hash. If they match, the record is authentic. There's no need to call a registrar or wait for an HR department to pick up the phone. This process allows for verifiable digital credentials to be shared without ever exposing the entire record to a third-party database. You get 100% certainty without the liability of data ownership.
Understanding Zero-Knowledge Proofs (ZKP) in Credentialing
ZKP is the ultimate tool for companies that value speed and security. It allows one party to prove to another that a statement is true without revealing any information beyond the validity of the statement itself. Zero-Knowledge Proofs are the holy grail of data privacy in 2026. Consider a bank verifying a customer's income. Instead of the customer handing over three months of sensitive bank statements, ZKP allows the user to prove "My monthly income is above $5,000" without the bank ever seeing a single transaction. This logic applies to credential data privacy across all sectors. You verify the attribute, not the data point. It's clean, it's fast, and it eliminates the risk of identity theft during the hiring or onboarding process.
The Role of Decentralized Identifiers (DIDs)
DIDs are the structural backbone of user-centric identity. Currently, 75% of online identities are managed by centralized giants like Google or LinkedIn. That's a single point of failure. DIDs change the power dynamic. They are a new type of identifier that enables verifiable, decentralized digital identity. They allow individuals to own their identity independent of any specific issuer or organization.
- Reduced Liability: You issue the credential, the user owns it, and the blockchain proves it. You don't have to secure the data forever.
- W3C Compliance: DIDs follow the W3C 1.0 standard, ensuring your credentials work across global borders without friction.
- Sovereignty: Users can revoke access to their data instantly, which is a core requirement for GDPR compliance.
By implementing these systems, you're not just checking a compliance box. You're building a scalable growth system that prioritizes trust. When you stop treating PII like a commodity and start treating it like a liability, your operational efficiency sky-rockets. Traditional databases are targets; decentralized systems are fortresses.

Compliance vs. Sovereignty: Evaluating Credential Management Systems
Compliance isn't a strategy; it's the bare minimum. Most firms brag about being GDPR compliant, but in the world of credential data privacy, that's just the floor. If your data sits in a centralized SaaS database, you've built a honeypot for hackers. A 2023 IBM report found the average cost of a data breach reached $4.45 million. Centralized platforms represent a single point of failure. When their security cracks, your users' entire professional identities go with it. You aren't just losing records; you're losing the trust that fuels your growth.
True sovereignty means the user owns the data, not the platform provider. Transitioning from traditional database storage to blockchain-anchored verification changes the ROI of your security spend. You don't store the sensitive PII (Personally Identifiable Information) on a public ledger. Instead, you store a cryptographic hash. This "Privacy by Design" framework ensures that even if a system is compromised, the actual credential remains secure. It's about shifting from "trust us with your data" to "verify the data yourself." Stop settling for systems that treat your users like digital tenants.
- Centralized SaaS: High risk, vendor lock-in, and a 100% dependency on the provider's firewall.
- Self-Sovereign Identity (SSI): Decouples the data from the provider, placing the keys in the user's hands.
- Blockchain Verification: Provides a tamper-proof timestamp without exposing the underlying personal details.
Navigating Global Regulations: GDPR, CCPA, and Beyond
Regulators don't care about your good intentions; they care about your audit trail. Under GDPR, the "Right to be Forgotten" seems at odds with an immutable blockchain. Smart architects solve this by keeping PII off-chain. You revoke the cryptographic pointer, making the data effectively invisible and useless to third parties. This satisfies the Utah Division of Technology Services on digital credential security standards, which emphasize using decentralized tech to slash fraud while protecting individual privacy. Data residency is another trap. 74% of organizations struggle with cross-border data transfers. Blockchain-based systems bypass this by letting the user carry their own data vault, regardless of where the physical server sits. It's a cleaner, more scalable way to handle global compliance without the legal headaches.
Interoperability: The Key to Long-Term Data Privacy
Walled gardens are where data goes to die. If your credentials only work inside one proprietary app, you've failed the utility test. This lack of interoperability forces users to create multiple accounts, which expands their attack surface and weakens credential data privacy across the board. You need to demand open standards like Open Badges 3.0 and W3C Verifiable Credentials. These protocols ensure that if your software provider goes bankrupt tomorrow, the credentials remain valid and private. 90% of legacy systems fail when the vendor disappears because the data is trapped. By using interoperable standards, you ensure the credential's lifecycle isn't tied to a single company's balance sheet. Don't lock your users into a silo. Build for a future where data moves freely but remains under the owner's total control. That's how you scale a reputation system that actually lasts in a volatile market.
5 Pillars of a Privacy-First Digital Credential Strategy
Compliance isn't a trophy; it's the bare minimum for staying in business. If your credentialing system treats data like an afterthought, you're building on quicksand. Real growth requires a framework that turns credential data privacy from a legal hurdle into a competitive advantage. You don't just need a "secure" system. You need a fortress designed for scalability and trust.
- Step 1: Data Minimization. Stop hoarding data you don't use. If a verifier only needs to know a student passed, don't give them their home address or birth date. Collect the absolute minimum required for the transaction. Every extra byte of PII is a liability that increases your attack surface.
- Step 2: Encryption at Rest and in Transit. This is non-negotiable. Use AES-256 for storage and TLS 1.3 for data movement. If your tech stack relies on outdated 2018 standards, you're already behind. Security isn't a feature; it's the foundation of your brand's integrity.
- Step 3: Granular Access Control. Identity management isn't a binary "yes" or "no." Implement role-based access control (RBAC) to ensure only authorized personnel see sensitive records. Use time-limited verification links that expire after 48 hours to prevent permanent data leaks.
- Step 4: Automated Revocation. Credentials aren't static. If a certification is invalidated or an employee leaves, the digital record must reflect that instantly. Use real-time status checks to ensure that revoked credentials don't provide a backdoor into your ecosystem.
- Step 5: User-Centric Design. Give the power back to the recipient. A privacy-first strategy allows users to choose what they share and with whom. When users own their data, they trust the platform. Trust drives adoption. Adoption drives profit.
Implementing Data Minimization in Certificate Design
Less is more when you're designing for 2024. A visual certificate should be a clean marketing tool, not a data dump. Move sensitive PII into encrypted metadata layers that only authorized verifiers can access. A 2023 pilot program for a major European tech certifier showed that moving 70% of PII from the visual layer to secure metadata reduced accidental data exposure incidents to zero. This approach keeps the design professional while keeping the credential data privacy standards airtight.
The Importance of White-Label Portals for Privacy Trust
Stop sending your users to third-party domains that harvest their data for "analytics." A white-label portal ensures the verification experience stays under your brand's roof. This isn't just about aesthetics; it's about control. By using your own secure portal, you eliminate third-party tracking cookies and keep user interactions private. Integrate your GDPR-compliant privacy notices directly into the digital locker. This transparency builds the kind of user confidence that translates into long-term retention and higher ROAS on your training programs.
Don't let legacy systems stall your expansion. If your current setup can't handle these pillars, it's time to upgrade to a system built for the modern economy. Stop managing liabilities and start scaling your results with VEC Digital's high-performance growth strategies.
Scaling with Confidence: How VEC Tech Automates Privacy-Compliant Issuance
Scaling manual certificate issuance is a recipe for disaster. If you're still handling PDFs via email, you're sitting on a privacy time bomb. VEC Tech LTD changes the math entirely. We've built the VEC Tech LTD Digital Locker to serve as a secure vault for professional achievements. It gives users total ownership of their data while ensuring your organization stays compliant without lifting a finger. This isn't just about storage; it's about building a reputation system that scales alongside your business goals.
Our API-first approach means you don't need a total system overhaul. We plug directly into your current LMS or HRIS stack. This integration ensures that credential data privacy isn't a manual checklist; it's baked into the digital workflow from the first byte. When you automate the pipeline, you eliminate the human error that leads to 82% of data breaches. You get a streamlined, secure process that works while you sleep, protecting both your brand and your graduates.
Verification used to take days of back-and-forth emails. Now it takes exactly three seconds. Every VEC Tech LTD credential features a unique, tamper-proof QR code. One scan confirms authenticity against our blockchain-backed ledger. You aren't just issuing a piece of paper; you're issuing a cryptographically secured asset that cannot be altered or forged. This level of security is non-negotiable in a market where 15% of professional claims are estimated to be fraudulent.
Scaling shouldn't increase your risk profile. Whether you're issuing 100 certificates or 1,000,000, the infrastructure remains rock solid. By moving to VEC Tech LTD, companies reduce administrative overhead by 65% within the first 90 days. You stop paying for manual labor and start investing in a system that grows with your ambitions. The ROI is clear: lower costs, zero fraud, and 100% compliance at any volume.
Enterprise-Grade Security Powered by Vision Tech Solutions
Vision Tech Solutions provides the backbone for our global infrastructure. We don't just follow GDPR; we exceed it by implementing zero-trust architecture across all data points. Our blockchain-backed authenticity ensures that credentials cannot be faked, period. This isn't a "security feature"; it's a fundamental shift in how trust is built in the digital age. We've optimized our servers to maintain 99.99% uptime, ensuring your credentials are always accessible. Plus, our white-labeling options mean your brand stays front and center. You get our world-class technology wrapped in your corporate identity, maintaining a seamless experience for your users.
Getting Started: From Paper to Profit in 30 Days
We don't believe in long, drawn-out implementations that stall your progress. Our onboarding process takes you from paper to profit in 30 days. We start with a deep dive into your current data architecture. We consult on how to structure your information to ensure maximum credential data privacy and operational efficiency. It's a low-friction transition designed for high-impact results. We handle the technical heavy lifting so your team can focus on growth. No more vanity metrics; just pure, scalable performance. Stop risking your data and start scaling your impact with VEC Tech LTD.
Stop Managing Liability and Start Scaling Trust
The era of "good enough" security is dead. By 2026, credential data privacy will separate market leaders from legacy failures. You can't scale a business on shaky foundations or vanity metrics. Real growth requires a system that turns PII into a secure, tamper-proof asset. We've seen enterprises cut credential fraud to near zero while reducing verification costs by 80% using blockchain-anchored technology. It's about protecting your bottom line and your reputation simultaneously. Data breaches cost companies an average of $4.45 million per incident in 2023. You don't have the budget to be another statistic.
VEC Tech, powered by Vision Tech Solutions DMCC, isn't here to offer vague advice. We provide a hard-coded infrastructure trusted by global universities and Tier-1 enterprises. Our platform automates the heavy lifting of privacy-compliant issuance so you can focus on ROAS and global expansion. Stop reacting to regulations and start dictating the industry standard. Your competitors are already moving. It's time to outpace them with a system built for the 2026 landscape and beyond.
Book a Demo: See How VEC Tech Protects Your Bottom Line
Let's build a future where your data is your strongest asset, not your biggest risk.
Frequently Asked Questions
Is blockchain-based credentialing compliant with GDPR?
Yes, blockchain-based credentialing is GDPR compliant if you use a hash-only on-chain approach. Storing PII directly on a public ledger violates Article 17, but VEC Tech protocols keep 100% of sensitive data off-chain. This architecture protects your credential data privacy by ensuring 0 bytes of personal data are immutable. You get the security of blockchain without the 20 million Euro penalty risk for non-compliance.
What happens to credential data privacy if the issuing platform goes out of business?
Your credential data remains accessible because we use decentralized identifiers and W3C standards. Unlike legacy systems where 40% of data is lost when a vendor shuts down, our architecture decouples the proof from the platform. The student owns their 256-bit encrypted file. Even if the issuer disappears, the verification link remains active and valid for life. We prioritize data portability to ensure long-term ROI.
Can a digital certificate be deleted if a student invokes their 'Right to be Forgotten'?
Yes, we fulfill Right to be Forgotten requests by deleting the off-chain data store linked to the blockchain hash. While the transaction record is permanent, the associated PII is erased within 72 hours of the request. This renders the on-chain hash useless and unidentifiable. It's a 100% effective way to maintain credential data privacy while respecting individual data sovereignty and meeting strict GDPR audit requirements.
How do I ensure that only authorized employers can see a candidate's credential data?
You control access through granular permission settings and private sharing links. Candidates decide exactly who views their records; employers only see the data points they're permitted to access. In 2023, 92% of data breaches occurred due to over-sharing. Our system prevents this by using encrypted view-only tokens that expire after a set period. This ensures zero unauthorized data leaks and maintains complete control over the sharing process.
What is the difference between data security and data privacy in credentialing?
Data security is the 256-bit encryption protecting the vault, while data privacy is the legal framework governing who holds the key. Security prevents 99.9% of external hacks. Privacy ensures that even the system administrators can't peek at student records without consent. In credentialing, you need both to scale your reputation and avoid the 4% global turnover fine associated with GDPR breaches. It's about protecting both your assets and your students.
Is it possible to forge a blockchain-verified digital certificate?
Forging a blockchain-verified certificate is mathematically impossible due to SHA-256 cryptographic hashing. A single character change in the document results in a completely different hash, which immediately fails verification. Traditional paper diplomas have a 15% fraud rate in some sectors. Our digital system reduces that fraud rate to 0%. This protects your brand's ROI and ensures that your institutional integrity is never compromised by bad actors.
How does VEC Tech handle the storage of sensitive student or employee PII?
VEC Tech stores PII in SOC 2 Type II compliant environments with AES-256 encryption. We never store personal details on the blockchain ledger itself. Instead, we use a pointer system where only a non-identifiable hash lives on-chain. This setup reduces the attack surface by 85% compared to centralized databases. Your team manages records through a secure dashboard while we handle the cryptographic heavy lifting in the background.
Do I need to be a blockchain expert to manage a private credentialing system?
You don't need any technical expertise to manage our system. We've built a no-code dashboard that handles the complex cryptography in the background. Your team focuses on issuing and scaling, while our API handles the heavy lifting. Implementation takes less than 14 days, allowing you to transition from legacy paper systems to a digital-first growth model without hiring a single developer or blockchain engineer.